History
What is History?
What is History? History is the systematic study and documentation of the human past. For Instance, my name is Anthony Joseph Hopkins and I was born on Thursday June 24, 1965 at 7:30pm. My mother’s name is Mary Lou’s Hopkins and my father’s name is Joseph Odell Webb. The hospital that I was born was St. Elizabeth Medical Center in Dayton, Ohio.
Next, I was living at the time with my two living grandmothers and aunt inside of a two bedroom house on West First Street in Dayton, Ohio. I remember when I was a child, I lived with my grandparents for several years. I went to Edison Elementary School. I want all of you to know that I was only a C average student. I attended Edison Elementary School from 1971-1979. I attended Franklin School for one year.
Further, I was a child who has experienced both physically and mentally as well as emotional abuse. I have five brothers and two sisters right now. I do recall getting chased home by my fair weather friends. During that period of my life, I do remember suffering from tuberculosis for nine years from 1976 to 1985. I had to take Ciphro Flacin twice per day for several years.
Moreover, I do remember watching television when President Richard Nixon resigned from government and the Vietnam War on television as well. Personally, I would rather be in school or my grandparents house instead of my mother’s house. I went to school and I got into fist fights with various people for several years. I do recall spending time with my half siblings. I was a latch key child for several years.
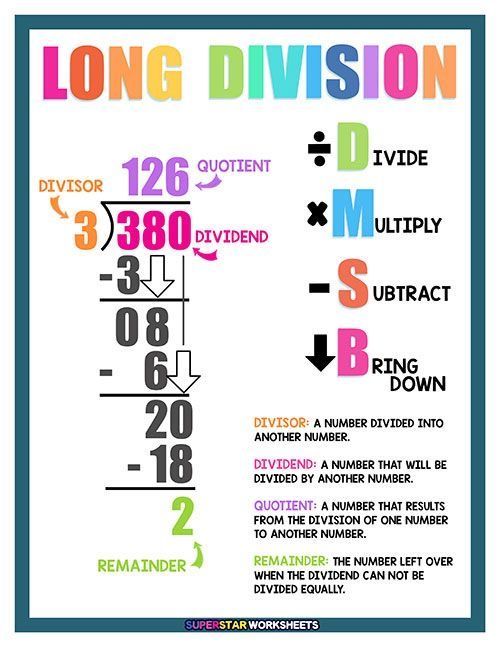
Also, I used to have problems with math. I did very well in my other classes. I do remember going to school just to eat breakfast and lunch only. Jesus Christ is my personal Savior. I have waivered in my faith in God. My personal history was rough. I was an extrovert and an introvert at the same time. I remember working for the Dayton Daily Newspaper Company for four years.
In Addition, I used to have bad teeth as a child and adult. I took better care of myself back then compared to right now. I had a lot of structure during that time. I am going to say this and mean it. I really need structure in my life right now. I want to say that I am a procrastinator. I am not a lazy person, but I tend to become complaisant. My history consists of playing sports. I played basketball with the YMCA for four years.
Currently, I have written three books for many years. My first book is called The Best of Anthony Hopkins. I wrote that book back in July of 2000. I have published two books with Authorhouse Publications. My second book is called My Grace is Sufficient for Me and my most recent book is called Essays. My books consists of essays that I have written based on my relationship with God.
In my personal life, I have been in and out of mental health institutions. For the past 28 years, I have suffered from Schizoid Affective Disorder and Schizophrenia. I am guilty of spending too much time by myself. For the past 31 years, I lost my great-grandmother. As soon as I saw her inside of a casket, I lost my mind. I knew that she was not coming back to life. I lost my family members, and I am devastated. I will admit that I have been hearing voices from people from my past.
Finally, I am 60 years old now and I am very depressed. I write a lot about my personal life. I rarely have visitors coming over my apartment. I want to inform all of you that my life is very important to me. I do remember that on Saturday, February 13, 2010, I tried to kill myself by taking all of my pills at one time. I almost died during that time. I will admit that I suffer from seizures. I have been suffering from seizures for 60 years now. I understand that a person relationship with God is more important than death itself. I graduated from high school and college at Paul Laurence Dunbar on Tuesday, June 10, 1986, and I graduated twice from the University of Toledo in 1993 & 1995. I do remember living in Toledo, Ohio, and Charlotte, NC. I remember working at the University of Toledo from 1992-1996. I worked at the University of North Carolina at Charlotte from 2001-2009. I have maintained a Counselor Assistant License from 1993-2010. I have had a good career as a youth counselor from 1993-1996.
In conclusion, I am a very intelligent man who has a lot of common sense. I am a person who has a lot of friends. I have both good friends and bad ones. I am losing my eyesight because I have suffered from glaucoma and cataracts from the 2005 present. I have suffered from Diabetes from 2015-present. I have suffered from Schizoid Affective Disorder from 1997-present. My history is not glamorous. I am just an average person who has a lot of debt. I owe the University of North Carolina at Charlotte a total of $30,000 dollars in student loans. I live in an apartment on the northwest side of Dayton, Ohio, from 2011 to the present. I am living on a fixed income, and I am still broke financially. I have no social life right now. I have an interest in working in a library again. Please Lord Jesus, hear my prayer. I really need you in my life right now. I have been clean and sober for 35 years now. My clean date is Wednesday May 2, 1990. History consists of the things that I do for Jesus Christ. If I am able to help others and communicate with Jesus Christ on a daily basis. I need to read His Word and demonstrate His deeds to mankind. Thank you for reading my story. God Bless You All.
A Prayer
Prayers
Characteristics of a Computer Hackers & Scammers from a Behavioral Perspective
Characteristics of Computer Hackers and Scammers
This is a very important blog that has a whole lot to do with the livelihood of people in our society. The characteristics of computer hackers and scammers are very serious because it has a lot to do with online communication. Whenever a person is online, they should always pay attention to the lies that each computer hacker and scammers tell to their victims. For instance, if a hacker or scammer indicated that they have done something for the person, it is not true. Another thing, is that they have a tendency to use a lot of misspelled words all of the time whenever they are typing.
A scammer always tries to beg and plead with the person they are online with to try to persuade them to do something all of the time. For example, if someone is sending money to a hacker or scammer; the hacker or scammer would tell them to send additional money. In my case, I ended up sending over $16,000 dollars in Western Union Funds to individuals who were on Black planet, Yahoo, and Face book. These websites are unsecure and you will have to use them at your own risk. When it comes to Mocospace, computer hackers and scammers are using women’s profiles on a daily basis without the person’s consent or knowledge. Therefore, it makes the female feel very uneasy and scared to be on the website.
There are other additional characteristics that everyone needs to be aware of is that; some of the hackers are located overseas. I want to inform everyone that computer hacking occurs worldwide. The behavior is also learned from each scammer and hacker. Most of the locations that the hackers are located at are in larger cities. This makes them very hard to find. If a person gets scammed by a scammer or hacker, always report it to law enforcement. If Western Union is involved, a fraud report must be filed immediately. This is by calling the toll free number and they will direct you to the fraud department. Always keep all of your receipts. By keeping your receipts, you will be able to file a report at an instance. All computer hackers and scammers use statements and misspelled words to confuse those they are online with.
If anyone suspects that a hacker is online with them, it is best to log off the website and file a cybercrimes report. A person must report the information to the Information Technology Department of that website as well as the cyber security department. Computer Hackers and Scammers always want your credit card information and social security number as well as your phone number. The reason why they want your phone number is because they want to keep in touch you on a regular basis. Scammers on the other hand, just simply take advantage of you without the use of a computer. Scammers as well as Hackers always have a lot of background noise whenever anyone is talking with them. Some of the Western Union Transactions that I have made with the people who scammed me were outside.
Whenever I received a phone call from the Scammers and Hackers, they usually called me each time I got paid from my jobs. From March 13, 2008, until February 3, 2010; I have sent a total of $16,977 dollars to people that I did not know. Most of my money went to one country, and that country is Ghana in Africa. Most of the Scammers and Computer Hackers tend to use the same women’s profiles and email addresses to communicate with those whom they are online with. The phone numbers themselves are easily cloned and duplicated as well as illegally transferred to another person’s cell phone number without the victim even knowing it.
Behaviorally
Computer Hackers lack empathy and sympathy for their own victims. These individuals are very opportunistic by nature. I know because I was only seeking an opportunity for a new relationship with a member of the opposite sex. These individuals were calling me each day of the week. These computer hackers are human beings. These people will smile while they are in your face and stab you behind your back. The average computer hacker is highly intelligent and they are computer savvy as well. An average computer hacker makes his or her money by using men who are not aware of the computer hackers’ schemes and tactics. Some computer hackers are very persuasive by nature. These people are like car salesmen. They will always keep on trying to convince you to buy their products. I know that 85 to 95% percent of the women’s profiles are being used by these computer hackers just to lure you in like a fish. I know because I was online with a female for a short period of time. She pretended to be from Accra Ghana in Africa. She recorded her voice on her laptop computer, and she stated to me that she wanted to get married to me personally. These women insist their computer hacking victims send them money through Western Union and MoneyGram Financial Systems. I want to inform everyone that these individuals live in the United States 🇺🇸 of America. These individuals usually tell their victims to send money to a foreign country, and they are receiving the interest from their bank accounts. Currently, they are telling everyone to send them money to a CashApp account that is in another person’s name. There are pyramid schemes being conducted each day of the week. I am telling everyone that the women who scammed me were living next door to me at Wentworth Hi Rise Apartments, located in Dayton, Ohio. CashApp is the usual method of transaction because it is very discreet. I am telling everyone that these individuals are currently living in the United States of America right now. Some of these men and women are spoofing and cloning phone numbers all of the time ⏲️. Some of these women are working at strip clubs nationwide and are prostitutes as well. Some of these women do not perform any acts of coitus for anything less than $500.00 dollars.
Computer Hacking and The Holy Bible
In Relation to the Bible:
“Thus says the LORD of hosts: ‘Execute true justice, Show mercy and compassion Everyone to his brother. Do not oppress the widow or the fatherless, The alien or the poor. Let none of you plan evil in his heart Against his brother.”
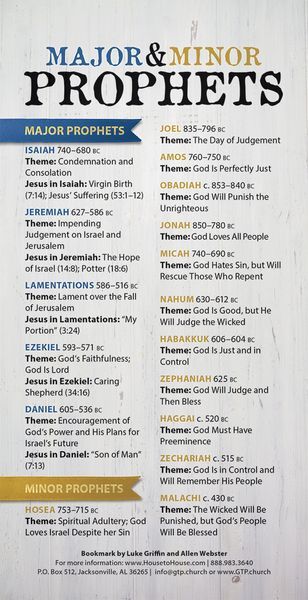
Zechariah 7:9-10
This verse from Zechariah explains how we as people, not just Christians, should treat other people around us daily. God is telling us that we should be respectful and be truthful in the things we do in our daily lives. Not only should be true to others, but to ourselves as well. In that sense, phishing is not correct by any means based on this passage.
Therefore, putting away lying, “Let each one of you speak truth with his neighbor,” for we are members of one another. “Be angry, and do not sin” : do not let the sun go down on your wrath, nor give place to the devil. Let him who stole steal no longer, but rather let him labor, working with his hands what is good, that he may have something to give him who has need.
Ephesians 4:25-28
This second passage explains to us that we should not lie to one another. Phishing is deliberately misleading someone else for a person’s own personal gain and essentially lying. Even if we are angry at someone else, we should not commit sin to fulfill these thoughts towards others. These verses also explain that we should change and try to be better in what we do each day.
Phishing is absolutely wrong. Nowhere in its concept is it morally or ethically right and there are many laws against it. It is very wrong to go and trick someone into something especially with some who is not very familiar with computers. It is almost as if you are taking candy from a baby, it is not hard to do it, but they can often not do anything about it. Phishing targets people who have very little information or knowledge about computers and sucks them into giving them information, which is then accessed and used. It is human nature to feel bad for someone who is being taken advantage of, and often we do what we can to help them. Just because someone has little knowledge about something doesn’t mean someone should be able to take advantage of them and trick them into do something they would otherwise not do. Phishing is wrong, and anyone who is caught phishing should suffer consequences.
I want to inform everyone that over 1,000,000,000,000,000 websites are utilized by computer hackers each day. I was online using my Mocospace account early this morning, and suddenly, I came across someone who I perceived as a woman chatting with me. It looked suspicious because when I looked on her profile, I found out that she was not logged on to the website. Usually, whenever a person is logged on to Mocospace, a green dot appears right next to their name. This occurred around 12:30AM. I checked the female’s profile, and it has been confirmed that she was not logged on to the site. She logged onto the website yesterday. I felt baffled and confused because I always thought that these women would be online. It turns out that the profile was hacked. Some tips that I have to offer all of you are as follows: Always check for the green dot to see if the person is officially on the website. Second, examine the profile to see how long the person was logged off. This is pertaining to mocospace. As far as Blackplanet.Com is concerned, always check the profile to see how long they have been logged off or on. On average, most female profiles are hacked online because the hackers themselves usually go undetected. Most of the countries that have this kind of activity are Africa, India, Jamaica, Cuba, Brazil, Kenya, Nigeria, and London England. Most of your hackers are usually between the ages of 18-75. There is a very small percentage of the profiles that the hackers have are cloned. They are duplicated, and the pictures themselves are copied by the hackers themselves. Hackers have a tendency to prey on innocent men who are online between the hours of 9:00PM-6:00AM. Most of the activity occurs between the hours of midnight and 5:00AM. Computer hackers who are living in other countries have a 7 to 12 hour start on Americans who are online. The time change makes the difference. When I got scammed 17 years ago, I did not know it. The scammers were using women’s profiles on Blackplanet, Yahoo, Facebook, and Twitter. Some of your computer hackers use profiles of younger women between the ages of 18-75. The profiles themselves are randomly selected. This is serious because an average man would think that he is talking to his female or male friend; when they are talking to a computer hacker and data thief. Data thieves usually collect social security numbers of innocent people, and as soon as your information is online, it is collected from the website and, in some cases, a third party. I am happy that they have Bible verses that pertain to my situation. In most cases, it is best to examine the information.
Computer Hacking and Phishing
Phishing
The Oxford pocket dictionary defines phishing as the activity of defrauding an online account holder of financial information by posing as a legitimate company. This is what phishing is known for now in today’s internet driven world but it was not always the case. Phishing actually predates computers. Some people did it over the phone for years and they called it social engineering.
So why would someone think of phishing some one? There is a simple reason: to exploit people. These people are commonly known as scam artists. What these phishers normally do is send out millions of scam emails posing as something or someone who they are not. Normally they hope for a few people who received the email to respond to them by clicking the fake website and provide them with financial and or personal information. Also, anyone who has an email address is at risk of being phished. People can increase their risk of being targeted if their email is posted on a forum or website. The people phishing can also get many more email addresses by using a spider. A spider is something that searches through many websites and saves an innumerable number of email addresses, every one it can find. So in a nut shell, phishing is very profitable for criminals because, they can attain millions of email addresses and potentially set them up for an attack at relatively no cost to themselves (Beal, 2006).
There are some key factors and elements that one needs to help recognize if they are being phished. This scam often has three key elements or factors that will come about when someone is planning an attack. First, when checking your email and looking to see who the email is sent from. It will often be from a legitimate company’s address. If the email address looks suspicious, then be wary, but this is an easy obstacle for phishers to climb over. It is very quick and easy for someone to change the “from field” in most email clients to trick the person receiving the emails. Second, the email almost always will contain very similar images or logos that have been copied off of the real company’s website. Third, upon opening the email, it will have a link along with the text saying you should click the following link to make sure the personal information is correct. When trying to determine if you are part of a phishing experiment, there are many little things you might want to notice. These include spelling errors and unknown email addresses in text, and often, the email headers can have absolutely nothing to do with the company that the email implies to the recipient (Beal, 2006).
Being aware of phishing is an important concept people should try to understand. First of all, you do not need to click the text or URL that is stated in the email. If you see a suspicious email, you should delete the email promptly. After deleting the email from your inbox, you should delete your trash can as well. Often, you can block the email addresses that are sending you these risky emails. If the message or email looks very legitimate, you still need to remember to never click the link or URL in the email. To make sure you are going to the website you anticipated, you should open up your web browser and type in the website manually. Then, proceed to type in your personal information on the legitimate website (Beal, 2006).
It is very important to know what to do if you do find a suspicious email that is targeting you to be phished. First, you should notify the company that there are suspicious emails in regard to their company. Often, companies will want to know if anyone is using this “phishing” technique with their company’s name. Also, if you find a phishing email, you should report the phishing to the Federal Trade Commission. Many local police and investigators also take care and deal with internet phishing (Beal, 2006).
Now that phishing is becoming more common, criminals and scam artists are finding newer ways of targeting innocent people. A new, but becoming more common way of targeting people is the use of phishing and malware combined. Malware makes it where someone has control of the computer being targeted. Social engineering is often a very big part of malware. So, how does someone get control using malware? People can get control by attaching harmful attachments through emails. In the end, the user of the computer will execute a harmful file or software, and then, from there, many different things can be downloaded. Even something as simple as accepting a license agreement can easily download and install malware. There is, however, a very slow and sometimes pain taking process of sorting through the megabytes of data that have been collected in this form of attaining information. By combining malware with phishing, much vulnerability exists. The vulnerabilities can turn into things such as worms, viruses, and getting personal information. People often do not realize the effect of malware and phishing and what it can turn into.
Men Women & Criminal Prosecution !
Women who are on the run have a tendency to hide with other criminals themselves. Over 50% of the women who are captured in the United States are with significant other who are not married to them. Oftentimes, women are hiding inside of other countries and cities just to avoid getting prosecuted. The statistics are according to the United States Department of Justice. Recent statistics also reveal that women who are on the run are around males with an extensive criminal record themselves. Women who are on the run even for minor offenses are more than likely to hide in other cities and deny the existence of their crimes. Both men and women are in denial when it comes to even having an involvement with the person that they are accused of hurting in the first place. Finally, what are the alternatives for these criminals? The answer is getting them to justice by getting the general public involved. Also, the media is an outlet when it comes to assisting in the efforts to capture criminals. The assistance of the media, law enforcement, and the general public is important. There is a sense of reluctance when it pertains to the general public getting involved in capturing criminals. Men and women alike who are responsible for committing crimes against humanity need to face justice. Women are more inclined to turn themselves into law enforcement because they feel safe and secure and relieved because at least the burden is completely off of their backs. The men that are with them are aiding and preventing these women from facing the people that they have wronged personally. The men are involved because they are harboring criminals. The men who are involved in criminal activities tend to be more nonchalant than women. Men are more apathetic, discontent, unconcerned for personal safety, and are reluctant to deal with their problems. Men are not cognizant of the circumstances and, in some cases, are not aware themselves that they have committed a crime. There are times when they talk about it boastfully: I am talking about men: as well as women, but they refuse to deal with their problems. The men and women who scammed me have already been reported to law enforcement. I have been scammed by criminals who were located in Accra Ghana, a city in Western Africa. I was responsible for sending almost $ 17,000 in Western Union Funds to people that I did not know! The criminals are responsible for using women’s pictures and profiles illegally each day. This is a crime in progress. The criminals who scammed me have not been captured. The criminals who are using women’s profiles are located worldwide. They also obtain credit cards from their victims on the internet. There are over 1,000,000,000,000 websites that there criminals use who scammed me. Their favorite websites are Facebook, Myspace, Mocospace, Yahoo, Blackplanet, MeetBlack People, and Match.Com. The phone numbers that online scammers and hackers use are private and / or unavailable. This online crime happens on a daily basis.
What DID U DO 4 GOD & 4 U?






What did You do for God and Yourself?
This essay will consists of questions and answers concerning what have you have done for God and Yourself. First of all, I would like to ask a very good question. What have you done for God and yourself lately? I am asking this question because I would like to gain some ideas and solutions on what others are doing in their personal life for God. We must apply God’s values in our daily lives. God is building your life that matters to God. God knows exactly what we are doing all of the time throughout our lives.
Man’s only hope is in Jesus Christ. We must evaluate our character on the outside as well as our personal testimony in order to make things right. In my case, I have been taking care of my family members and friends by paying for their phone bills and feeding them. I have to be more responsible for paying my tithes and offerings to my own church. I will also admit that I have to put into my budget the money for tithes to my church at Fort McKinley United Methodist Church in Dayton, Ohio. I also will admit that my bills are more than what I pay for in groceries each month. My rent, phone bills and life insurance costs more than any of my bills.
Further, I would like to inform all of you that we need to give an account to God. God speaks though His magnificent creation. Psalms 37:4 says that we are delighted in the Lord. We are supposed to obey God’s word and know Him and experience Him in our lives. God is interested in my character. God is interested in my character because this is exactly what I am taking with me to heaven. I will not take anything else with me whenever I die and be with the Lord. God is evaluating our character while we are on earth. We have to put the man or woman together first and foremost. In Matthew the 22nd Chapter, it states that we must love God with all of your heart, soul, mind and strength. The second is just like it, we must love your neighbor as yourself.
Moreover, you will be able to put the entire puzzled together. God has been putting us together for over 2,000 years now. We cannot live by the world’s pressures. A responsible life is when we are doing God’s Will. God is watching us. Everything is open in front of Him. Life is a test of responsibility. God is also testing your responsibility, character, and values. God gives us a choice when it comes to our free will. However, in my case, I am not looking back into the world for anything that I need. In Psalms 107, it says let the redeemer of the Lord say so. We are living and walking testimonies of Jesus Christ. Our conduct, character, and testimony is the same to God. John 7:24 says be honest in your judgement and do not glance.
The Kingdom of God is inside of us. The kingdom of God is inside of our heart. We must be absolutely true when it comes to Jesus Christ.
Also, in 2nd Timothy 1:13 states that we are supposed to retain and hold to a high standard. Guard and treasure the Holy Spirit. We also must guard our testimonies and treasure it. We are living walking expressions of Jesus Christ. Jesus is the Son of the Living God. He is the eternal Son of God. Jesus is the full atonement of God. I believe that Jesus Christ is the Son of God. He died for my sins and the sins of the world. He is the subject of salvation. God put you on earth for 2 reasons. 1. To get to k now Jesus Christ through the Father. 2. God wants you to love Him. Your greatest gift is responsibility. How do you respond to stress, freedom, and the choices that we choose to handle responsibility? Personal responsibility is derived from character and choices.
Finally, we must put more emphasis on values. We must also emphasize self-control, love, understanding, and wisdom. I will admit that I used to be a person who blamed all of my problems on others instead of looking at my own behavior. Some would say that we are a nation of victims. If you look at your own role in your own behavior, then you would not be able to claim the title of victim. There are those who would say that Americans are a nation of entitlement. This means that the American character is the process of blaming people for your problems. We are supposed to live your life in a responsible way. I would say that I have been a very responsible person from the time that I was 7 years old. The victim mentality is when a person says that it is not my fault. The decay of the American culture is this sort of mentality. This obsession affects our way of thinking. We tend to hear more about choice.